EXPLORE ARTWORKS
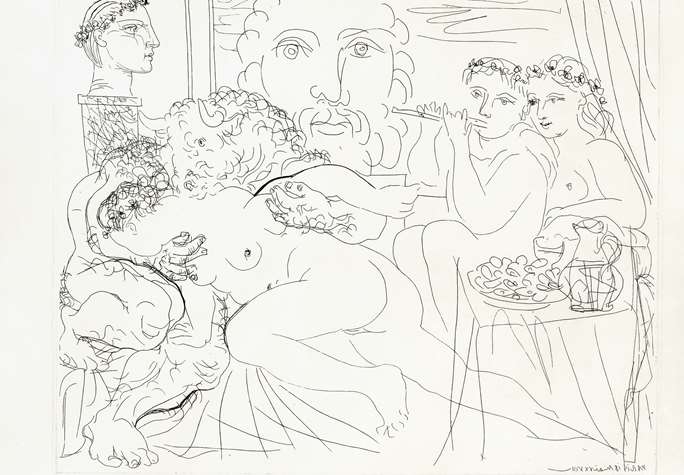
From Old Masters to Picasso, Louis XVI silverware to Art Deco cutlery, what you will find on MasterArt is a cut above the rest.
FIND TOP GALLERIES
MasterArt portal features long-established galleries and dealers, with solid reputations in the art trade, and whom regularly participate in prestigious international art and antique fairs.
READ ART PUBLICATIONS
Peruse richly illustrated, electronic catalogues and art books posted by galleries and dealers.
DISCOVER ART FAIRS
View our agenda to see MasterArt's selection of upcoming international art and antiques fairs, exhibitions and events.
Featured Artworks

Cohen & Cohen
Chinese export porcelain tobacco leaf meatdish

Sycomore Ancient Art
Pectoral ornament in the shape of a bouncing animal
Ronny Van De Velde
Dubbel portret van Henk en Nel Wiegersma (Double portrait de Henk et Nel Wiegersma), 1930
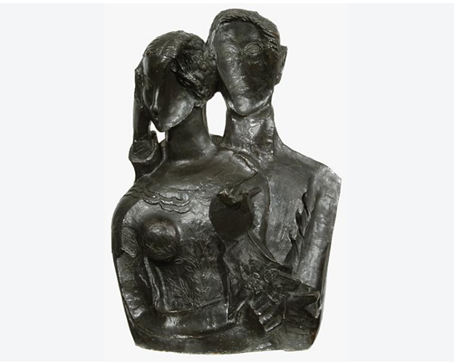
Ossip Zadkine (1890 - 1967)

S.J. Phillips Ltd
Mid-20th century two colour tracelink chain necklace, c.1940, testing as 18ct rose gold and platinum

Godson & Coles
A RARE GEORGE II PERIOD LACQUER BUREAU CABINET
MEET OUR GALLERIES
E.H. Ariëns Kappers
Founded in 1980 by art historian Erik Ariëns Kappers in the now famous Spiegelkwartier in Amsterdam, neighbour of the Ri...

L'Arc en Seine
Founded in 1984 by Christian Boutonnet and Rafael Ortiz, l'Arc en Seine is an essential reference in the field of Art De...

Godson & Coles
Godson & Coles have been established in London for over 30 years and specialise in the finest English furniture from the...

ABOUT MASTERART
The Online Platform for Collectors, Connoisseurs and Art Lovers alike
Whether you are looking for a specific work or simply indulging in a leisurely browse, MasterArt will guide you through a treasure trove of artworks, antiques and antiquities… and perhaps help you to find that rare piece missing in your collection!





















